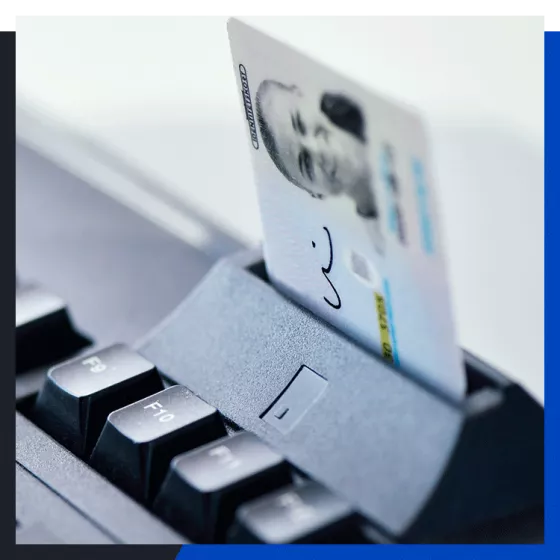
A complete solution

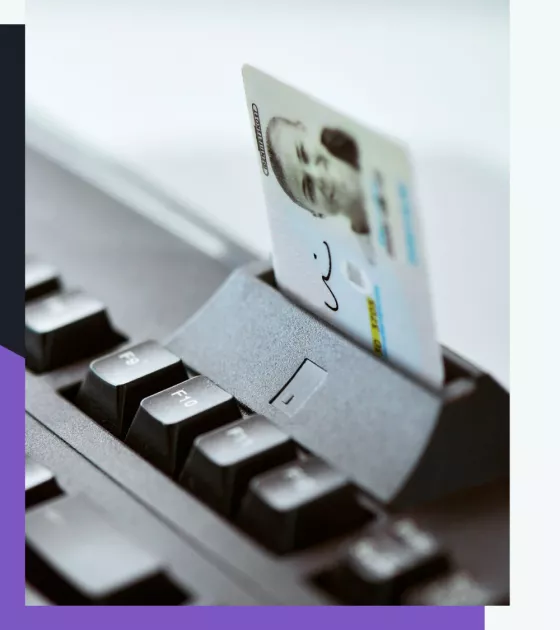
Net iD is a complete Public Key Infrastructure (PKI) solution. It includes everything you need to start using certificate based security on all your devices.
Secure all your devices and applications with the highest level of security.
Supports all types of clients
Lifecycle management of all tokens and certificates
Fully customizable for your needs